

Cloud computing is gaining traction and, with major cloud players establishing – or committing to – a local presence, it’s only a matter of time before every business has some, if not all, applications running in the cloud. For many organisations, concerns around cloud security are hindering their plans to move to cloud environments.
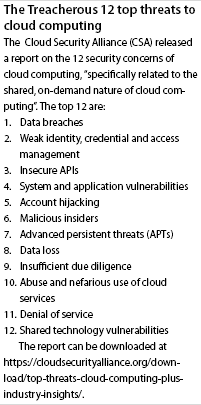
Fortinet’s most recent Global Enterprise Security Survey states that 74% of surveyed organisations believe that migration to the cloud will make cloud security a growing priority in the future. The fears around security in the cloud are hardly surprising when faced with the threats listed in Cloud Security Alliance’s (CSAs) Treacherous 12 Top Threats to Cloud Computing Plus: Industry Insights report (See box).
However, businesses that have the right policies and processes in place to protect their own data, both in the cloud and travelling to and from the cloud, shouldn’t let security threats hamper their cloud strategies.
It’s true that many new threats have emerged as more businesses take to the cloud, however, most of these threats can be avoided simply by having sufficient controls in place. For many organisations, storing data and running applications on infrastructure that they don’t manage equates to vulnerabilities.
But because it’s the cloud provider’s business to store their data and host their applications, they typically have more security and security skills than most businesses do for their on premise solutions. It’s their business to invest in protecting their customers’ assets.
Data protection
One of the biggest misconceptions around cloud security lies around who is responsible for data protection: the customer or the cloud provider? While the cloud provider is responsible for ensuring their infrastructure is secure, the onus falls on the customer to ensure their data is protected and that the cloud provider’s security measures align with the customer’s security requirements.
Businesses retain the responsibility for what they put in the cloud and how they access it. In addition, customers put a lot of data into the cloud and assume that the data is protected without taking into account the number of access ports they have and who uses them. Stringent identity, credential and access management is a must.
Organisations need to check that their cloud provider’s security is aligned with their own policies to ensure proper data protection. It’s important to know where the customer’s security responsibility ends, and where the cloud providers begin to ensure that there is no scope for data loss or potential for data breaches. Organisations can then fill in the gaps effectively wherever the cloud provider doesn’t provide adequate security in terms of the business’s security policy.
While the cloud is an unquestionable enablement tool for businesses, making life easier in terms of accessibility, increased productivity and a score of other benefits, it also makes IT teams’ jobs considerably more complex.
Policy is essential
In the cloud, IT teams are no longer wholly in control of the data they are responsible for protecting, so it’s up to them to ensure that they implement and enforce data and cybersecurity policies, processes and procedures to maintain as much control as possible. It’s imperative that they not only apply these policies, but that they update them regularly and create awareness of security parameters among all users.
Included in the policy, businesses should have a strong focus on identity, credential and access management regardless of whether they embrace a public, private or hybrid cloud strategy. They also need to provide for backup, through a separate provider in the unlikely event that the cloud provider does not offer this as an add-on service.
Moreover, businesses should do a proper, full scale assessment of their current security measures and compare it with their chosen cloud provider, then work hand-in-hand with the provider to cover every aspect of security. Often, they will find their existing security falls short of that of the cloud provider, however they will also often realise the importance of access control.
Cloud usually provides authentication; however, a line needs to be drawn between the limits of the cloud provider’s authentication tools and the business’s own access requirements. A policy is essential.
Although regulations are coming into play that enforce the need for data protection, they also call for strict policies around data management and security.
It’s up to the business to protect its own data. What you put into the cloud, you get out, so part of the solution is to ensure that you know what data you are putting into the cloud, define the parameters and policies around keeping it safe, then ensure they are supplemented with suitable security technologies. With this in place, unless cloud offers no other benefit, there is no reason why any organisation shouldn’t be considering – and using – the cloud going forward.
For more information contact Commvault, skeating@commvault.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.