

Blok Developments is an urban property developer operating in Cape Town’s Atlantic Seaboard and CBD. Its thoughtfully designed and detail orientated apartments are built to make a lasting contribution to the neighbourhoods they develop in.
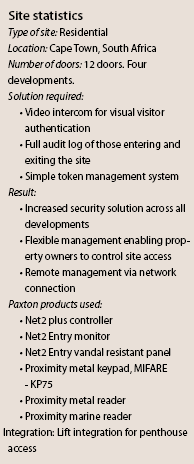
Security is a priority for Blok and its residents. It required a system that would allow it to control who could access the developments, and had the functionality to easily assign, update and bar access tokens, from a simple, reliable user interface. Blok also needed residents to have the option to visually identify visitors via video intercom.
Solid Systems, a managed IT service provider based in Cape Town was approached by Blok to install a security solution that met the requirements on their four new developments.
Solid Systems recommended Net2, Paxton’s flagship access control system, to control the access on site. It also included a Net2 Entry monitor, Paxton’s intuitive, colour touchscreen internal monitor, in every property for visual authentication and a direct line of communication to the security desk.
Net2 is a user friendly and flexible networked access control system, designed to make the management of any site straightforward. Net2, combined with Paxton’s plug-and-play door entry solution, Net2 Entry, has provided Blok Developments and its residents with a simple security system that is managed remotely by Solid Systems.
Solid Systems will manage and maintain the system on behalf of Blok, programming access control tokens and monitoring the system remotely. Michael Claxton, MD at Solid Systems says: “Our network management solution pro-actively detects issues within the Blok ICT environment, and attempts to resolve the issue automatically. If unsuccessful, a certified IT professional is notified and assigned to the issue for a speedy resolution.”
In place of traditional locks and keys, the residents now use tokens to access the site. If a token is lost, it can easily be barred from the Net2 system. New tokens can be added, and access permissions can be updated with ease. The use of individual tokens also provides Blok’s security personnel with a full audit log of who has entered and exited the developments, further enforcing the level of security for their residents.
The penthouse residents present their token upon entering the lift, which will then take them directly into their property.
| Tel: | +27 21 427 6691 |
| Email: | support@paxtonaccess.co.za |
| www: | www.paxton-access.com/za |
| Articles: | More information and articles about Paxton |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.