
We have all heard distributors talk about and label themselves as Value Added Distributors. What exactly is a Value Added Distributor and why is it relevant to consultants, system integrators and end users?
Do distributors have the appropriate pedigree and mix of product at the correct prices on their shelves? Do they provide training, pre-sales design skills, post sales deployment and support services? Are they providing credit lines or finance options? Do they have a national footprint that ensures streamlined operations and logistics to service market demand? Do they facilitate deal registration and commercial know-how to guide channel partners and negotiate with vendor-suppliers? Are repairs or product swap out facilities available for faulty items? The list goes on, but inevitably leads to a single truth. Just about everyone nowadays is adding some or all of these elements into the bag and calling it value add.
The fact is that when either a consultant, a system integrator or an end user walks into a room and Sentronics is standing next to all the other distributors, what gives either of these three target contact markets a compelling reason to decide to do business through this channel rather than through the opposition? Value Added Distribution has become a diluted term and a word used casually by any distributor whether they add value or not.
So how do we position against the risk of price pressure, still offer the best pricing, but also enhance our overall value offer? The answer according to Sentronics is to make available tools, services and intellectual property that enhance the value of our product offer to market through the supply chain, from consulting engineers through to system integrators.
Business relevance
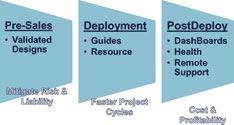
Essentially our services offer aims to enhance channel value by providing you with everything you cannot provide for yourself. The offer is segmented into three layers:
* Pre-Sales.
- Validated Designs.
* Deployment.
- Guides & Resource.
* Post Deployment.
- Health Maintenance.
Being able to bring together vendors such as Sony, Geutebrück, SAFLEC and Virdi we are able to design integrated security solutions that will carry Sentronics’ and the vendor stamp of approval. In other words, combining expertise from our end and from the end of the vendor we are able to validate the designs and provide a stamp of approval that should you use our validated design, the solution is guaranteed to work.
Once a validated design is specified in an official document the consulting engineer is automatically de-risked from certain liabilities usually exposed to. It also provides uniformed requests to market in terms of gathering information and pricing from system integrators to ensure apples are compared to apples.
When deployment occurs we will provide a deployment guide and physical engineering resource to not only perform deployment of the system by way of a step by step guide, but also ensure that the appropriate knowledge handover occurs to the relevant technical resources at an SI end. Deployment guides against validated designs ensure that the last step in the process is guaranteeing user acceptance and sign off.
Of course, the knowledge is handed over to the SI and this means that SI owns the site rather than a technical resource at distribution level. Along with this the site deployment time is much faster and the risk to the SI mitigated due to the deployment guides.
Now that deployment is complete and user acceptance and sign-off is ensured you can simply link your site by way of secure VPN tunnelling back into our 24/7-365 operation centre. We will not be performing video monitoring of these sites; therefore a simple amount of bandwidth is required. What we will offer however are the following subscription services:
* Digital dashboards.
* Health monitoring and reporting.
* Remote diagnostics and support.
Conclusion
Over the next few weeks Sentronics will run an information sharing campaign with end-user verticals, consulting engineers and system integrators alike to define the exact scope of what you require and to tweak the price to market for these services against you and the industry as a whole.
We will be building our operational space and ensure you visit us for a demonstration of what we can do for your business or that of your clients.
We will then further our offer to market to include the following services:
* Asset replacement registers.
* Network readiness assessments.
* Data security checks that validate secure video delivery from one device or VLAN to another.
* Increased granularity to include network and application performance monitoring and reporting.
* Services that collect data and provide auditing services through independent security auditing initiatives.
* Eventually start creating standards in the security space that relay back into barriers to entry for consultants and integrators so end users have a better experience.
For more information contact Sentronics, +27 (0)11 312 4147, michelle.korff@sentronics.co.za, www.sentronics.co.za

© Technews Publishing (Pty) Ltd. | All Rights Reserved.