
In 2013 IHS announced the rise of HD video surveillance was leading to an astonishing 413 petabytes of data a day produced by newly installed video surveillance cameras. Now, the proliferation of higher and higher resolution cameras means that the data deluge continues to increase.
566 petabytes was the amount of data produced in just one day by all the new video surveillance cameras installed worldwide in 2015. (One petabyte = 1024 terabytes, or around one million gigabytes.)

Just how much data is 566 petabytes:
• 11.3 million standard double-layer Blu-Ray movie disks.
• All Netflix’s current (as of December 2015) users streaming 1.2 hours of ultra-high definition content simultaneously.
• Approaching twice the amount of all user data stored by Facebook.
Why this increase?
Globally speaking, the video surveillance market is still not saturated. A recent IHS report on the installed base for video surveillance equipment suggested that there was one camera installed for every twenty-nine people on the planet. However, camera density varied drastically by country. The mature markets of the US and the UK had one camera installed for every eight and eleven people respectively. Emerging markets such as India (one for every 150) or Middle East and Africa (one for every 200) will see many new installations.
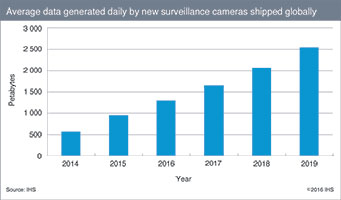
As well as new installations, retrofits and upgrades are a significant part of the market, a market which globally is expected to see a CAGR of 20% in new camera unit shipments from 2014 to 2019. In addition to the high demand for surveillance cameras, the following is also true:
• HD compliant 1080p 25/30 fps cameras have established themselves as the minimum expected from new cameras. This is not now limited to network cameras, HD CCTV has emerged as the replacement for many remaining standard definition analogue cameras.
• Panoramic and 4K cameras are two further storage hungry high-growth product categories.
• When video surveillance footage is being stored, it is generally being retained for an increasing period of time. Aside from out-and-out security purposes, video surveillance footage is being increasingly retained longer for anti-litigation, insurance and operational purposes too.
The amount of data produced by video surveillance cameras is huge, yet it is often overlooked in analyses of general worldwide data production and storage. The video surveillance industry is still somewhat below the radar for those involved in data storage, perhaps due to its challenges and characteristics.
Management and storage of potentially hundreds of high resolution video streams can be one such challenge. A large throughput capacity and a heavy write focus are just two characteristics of enterprise storage tailored for video surveillance workloads.
The traditional separation of security and IT has meant convergence between the two has been slow. However, increased surveillance storage demands may force many end-users to re-assess their storage solutions as previous approaches will no longer be sufficient. If enterprise storage is used, the majority of demand at present is being fulfilled by IP SANs.
Chinese video surveillance vendors are well positioned to ramp-up their offerings of low-priced, high capacity SAN systems to meet the capacity requirements of the mass video surveillance market. This approach, previously reserved for only the largest installations, is filtering down to smaller systems. However, the market is also evolving.
Concurrently, some larger installations have progressed to the use of smarter storage architectures integrating moving data between edge and core storage, between multiple tiers (in some cases storage media) within single platforms which are all viewable in the VMS. Current IT megatrends such as hyper-convergence, virtualisation and software defined storage are still a long way off from affecting the majority of video surveillance installations.
Yet, improvements in the efficiency of how recorded footage is managed throughout its lifetime are beginning to drive new approaches to video surveillance storage design. This is critical to keep up with the video surveillance data deluge.
For more information contact Josh Woodhouse, senior market analyst - video surveillance, IHS Technology, +44 1933 402 255, josh.woodhouse@ihs.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.