
Modern day electronics, appliances and equipment need consistent and clean power. Surges on the power input can damage your favourite music system or any other electrical device either by a single surge or by multiple surges over time. In the mid 1990s a European Study by Unipede found that 80% of all surges have an amplitude of up to 1,2 kV and have a duration of 1 to 10 micro-seconds. At the time, these surges occurred more than 10 times per day and were caused from multiple sources on the power grid. This is on a power grid that is considered stable.
Damage from surges can be classified as follows:
1. Hard failures. This permanent damage is caused by a single surge of significant amplitude. This is typical of lightning surges.
2. System interruptions. This is a temporary malfunction that can be rectified by cycling the power of the equipment and no permanent damage occurs.
3. Latent failures. This type of damage is the most disputed by insurance providers and occurs from continuous exposure to transients (surges) and Electromagnetic Interference (EMI) or Radio Frequency Interference (RFI). These surges erode the performance of electronic equipment and eventually cause permanent damage. Typically this damage is caused by surges from the utility power provider or inductive loads such as motors on the property. EMI/RFI are the most under-protected type of surge and require an active sine wave tracking surge protection device.
What type of surge protection do you need?
BFR Digital’s single phase and 3-phase surge protection devices incorporate a hybrid topology.
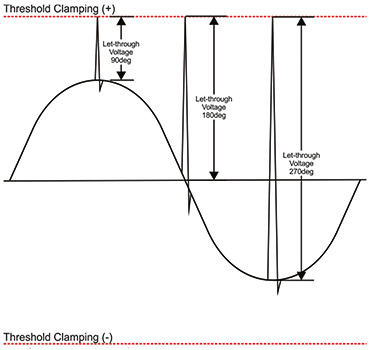
1. Threshold Clamping Technology. This is traditional surge protection technology where surges are clamped once the threshold of a Metal Oxide Varistor (MOV) is reached.
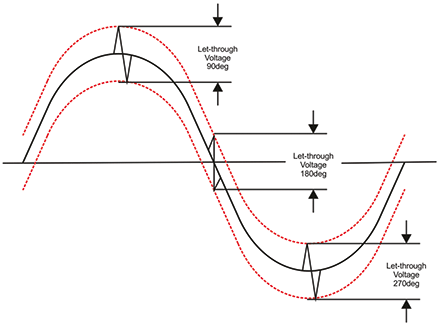
2. Sine Wave Tracking Technology. This technology is active surge protection and:
a. Suppresses high frequency, low energy ring wave surges (transients) at any phase angle that the surge may occur. This is typical of loads that generate a back EMF.
b. Suppresses RFI and EMI.
c. With conventional light bulbs being replaced with LED bulbs, household appliances being fitted with energy saving electronics instead of mechanical controls and the use of inverters has led to EMC (Electromagnetic Compatibility) interference. Sine wave tracking surge protection suppresses the noise generated by EMC related interference.
BFR Digital has incorporated these two technologies in a single device allowing for effective active protection against lightning surges, power utility generated surges, RFI, EMI and EMC transients.
After numerous requests for a product that does not need an electrician to install we have just launched a new Inline Sine Wave Tracking Surge Protector. This inline unit is a simple plugin professional device. There is also a short video available at www.bfrdigital.co.za/1_phase.html
For more information, contact James, BFR Digital, +27 (0)11 786 5575, jamesf@bfrdigital.co.za

© Technews Publishing (Pty) Ltd. | All Rights Reserved.