
Universities, their staff and students experienced violence, abuse and intimidation in nearly 40 countries between January 2009 and February 2013, according to the report Institutional Autonomy and the Protection of Higher Education from Attack, commissioned by the Global Coalition to Protect Education from Attack (GCPEA).
There is no doubt that safe and secure campuses are better learning environments for students. Not only do they assist in the attraction and retention of highly qualified and competent faculty members and administrators, but they also help to prevent theft and vandalism, which in turn frees up funds for other initiatives.
Sadly, many tertiary educational facilities have no idea where to begin with an integrated and scalable security solution. In a report published in the Campus Safety Yearbook (2013) it was noted that 41% of survey respondents struggle with visitor management and 50% of the facilities cannot lock down more than 75% of their campuses. In addition, 39% said that their video surveillance systems are not integrated with physical access control and 33% have radio systems that cannot interoperate with the first responder’s radio systems.
Jack Edery, CEO of Elvey, says that a sustainable security solution should consider all elements to prevent both theft and to moderate vandalism and violence from external and internal sources. The challenges are many, with the sheer size of most university campuses being top of the list. Add to this the daily influx of a variety of visitors, as well as controlling stadiums, cafeterias, on-campus residence facilities, event venues and parking garages, and the logistics clearly become an overriding issue.
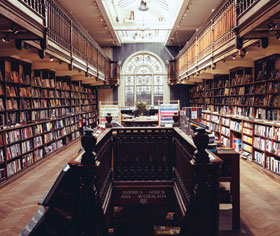
Edery suggests a combination of security technologies that include perimeter surveillance and access control, licence plate recognition cameras, on-campus surveillance, access control into facilities – including lecture rooms, cafeterias, dorms/residences, libraries, IT rooms and administration blocks – intruder detection as well as fire monitoring and control. Critical to the success of these systems is that they can be upgraded with ease, can be integrated with each other for a unified solution and are linked to an incident response mechanism.
Elvey has adopted a best practice approach to campus security that aims to alleviate all potential risks. Synergistic technologies include intruder detection, access control, surveillance systems and fire control systems, with a number of hardwired and wireless options available for each specific application and client. Examples include the Impro portal system with its visitor portal abilities and integrated biometric units such as Suprema and Sagem. On the video surveillance side, Elvey places emphasis on Arecont HD IP cameras and the Cathexis monitoring backbone with video analytics capabilities.
Edery says that it is important to ensure that the technologies being supplied are complementary and able to work together as a total solution. In addition, educational facilities should select an installer or system integrator that has a definable track record backed by successful client references. The best approach to ensuring a sustainable security solution is for educational facilities to confer with management of other educational facilities where systems have been effectively implemented.
For more information contact Elvey Security Technologies, +27 (0)11 401 6700, info@elvey.co.za, www.elvey.co.za
| Tel: | +27 11 401 6700 |
| Email: | info@elvey.co.za |
| www: | www.elvey.co.za |
| Articles: | More information and articles about Elvey Security Technologies |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.