
According to IHS Technology, the access control industry could begin to see rapid changes in the short to medium term. In an historically slow moving market (compared with video surveillance) the access control market has seen many new entrants, such as Axis, as well as new end-user demand from the residential space and continued adoption of newer technologies such as wireless electronic locks.
IHS expects that the market size for electronic access control will top $3,5 billion in 2014, driven by returning growth in the Americas market as well as emerging regions such as Middle East and Africa.
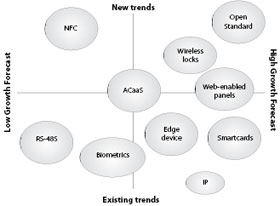
For hardware, much of the growth will be driven by electronic locks which can either be offline-standalone, data on card or wireless-online. Wireless continues to see strong growth as end-users begin to trust and understand the technology. Additionally, IT departments are more involved than in the past and will likely continue to be heavily involved and in some cases, may begin to manage and dictate access control installations.
IHS also expects that open standards will begin to take shape for the access control industry in 2014 although widespread adoption may take a few more years. Prior to investing in the R&D, many suppliers are waiting to see how the rest of the industry will adopt and implement standards. Other trends such as NFC continue to garner interest; however, adoption hasn’t been as extensive as originally expected. According to IHS, NFC has not yet been installed for access control purposes and some manufacturers are beginning to look toward other options such as Bluetooth low energy (BLE). Lastly, IP devices are seeing more uptake and are being pushed closer to the edge, allowing for more remote management and reducing installation costs.
Overall, this is an exciting time for the access control industry. With continued interest in big data, many are wondering how access control can be leveraged to harness some of this information which is leading to more seamless integrations.
For more information contact IHS, +1 512 582 2023, blake.kozak@ihs.com, www.ihs.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.