
South African businesses are most affected by crypto mining attacks by self-spreading malware, coin miner modules and infections spread via users downloading a ‘cracked’ version of legitimate software.
‘Living off the land’ attacks are also on the increase, with cybercriminals using legitimate tools to camouflage their incremental malicious activity over time, not unlike someone secretly getting your Wi-Fi password and using your connectivity, only with more malicious intent.
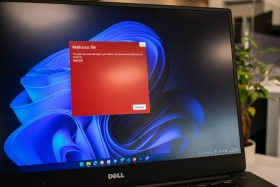
Ransomware attacks are not the most common of cybercrime incidents, but they’re still worth worrying about because of their significant impact on victims.

That’s according to Carlo Bolzonello, country manager for Trellix in South Africa, a cybercrime detection and response platform that uses machine learning and automation to help businesses respond to cyber threats quickly and effectively.
“Many of the attacks we see are operated by well-established groups that are always adapting and finding new clever ways to attack their victims. They are built and run like regular businesses, but their work is to find IT environments that aren’t properly protected. They then see how they can extract money, or other assets like intellectual property or identification data for resale,” Bolzonello says.
“Knowing these organisations and understanding their inner workings is the first step to preventing future security incidents, but with a constant drumbeat of security alerts, South Africa’s in-house cybersecurity teams are often overwhelmed by the number and diversity of attacks that affect their networks and ecosystems.”
With many security operations centres (SOCs) having a range of security products at their disposal, it can be complex to work through each solution’s protocols before identifying a threat and plotting a plan of action to counteract it – even with the help of online virus search engine tools.
“Having access to all the information about a particular threat on one dashboard helps the SOC team assess whether they can handle it on their own, or whether they need to call in the support and expertise of their colleagues in networking or the cloud team and activate a full war-room scenario,” he says. “It also helps them decide on whether to alert the C-suite about an attack and its consequences, so that the whole company can be alerted and prepared, or whether the threat is isolated to just one user (endpoint), where it can be halted.”
Bolzonello adds that many organisations have a variety of different security tools, with each responding to a different type of threat, or having been installed in response to a particular set of circumstances. Having all tools integrated into one dashboard helps remove a lot of the ‘noise’ of so many platforms highlighting potential threats – and allows the SOC team to actually look at the real threats and then identify how to respond to them.
That single dashboard can show where a threat has emerged and where it has spread to, so that action can be taken, immediately. It can reveal whether ransomware has gained access via a ‘recruitment’ email sent to executives, whether a ‘living off the land’ binary has taken hold via a download of an illicit copy of a movie, or whether a coin miner module has inserted itself via pirated software. Having this information to hand helps the SOC design and implement a quick and effective response, to stop the attack spreading further and to prevent it costing money for people and businesses.
“Not having that instant view into the situation means that it takes longer to address the issue, escalating the damage it causes and increases the costs of resolving it,” Bolzonello explains. “Having to call in security experts to first engage with the various solutions, a business may have to try to identify the issue, its location and its source, at a high hourly rate. That’s before you’ve calculated the costs of not being able to do business and the damage to your reputation.
“Having access to global threat monitoring that prioritises risks and proactively addresses vulnerabilities helps SOCs adapt, stay agile and respond to active threats. Doing so via an extended detection and response (XDR) that uses machine learning and automation makes it possible to recalibrate detection and prevention policies and strategies as threats emerge, across endpoints, infrastructure, cloud, users and data,” he says. “It’s a living form of security in the face of threat actors that helps SOCs configure their systems for their needs, in real-time, empowering them to work more effectively and efficiently.
Find out more at https://trellix.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.