
Abloy Oy today announced ABLOY CUMULUS, a platform for keyless access, combining hardware products with secure access and management applications. It brings all the solutions together into a single ecosystem with a risk-free, integrated cloud service.
“CUMULUS is our next step in ‘keyvolution’ in which mechanical keys are transforming into digital ones. We have wrapped our more than 100 years of security expertise into digital solutions for connected access management,” said Jussi Ahvalo, vice president, international sales, Abloy.
The key to keyless access
The world is becoming keyless, access rights are going digital and customers want everything to be integratable. Many property owners and managers are planning to switch to access management that is seamlessly location-independent, while securing all their keyless access points.
CUMULUS ensures secure access in commercial real-estate, public spaces, housing and sites essential for the functioning of society. It offers interfaces for third-party applications and software development. The CUMULUS range of keyless, online access solutions – from mobile keys and padlocks to upcoming electric locks and controllers – can be administered with any software tool that best suits the customers’ needs. By selecting ABLOY OS INCEDO, the organisation can also manage other ABLOY solutions with the same tool, such as electromechanical PROTEC2 CLIQ and mechanical keys.
“CUMULUS minimises management risks and provides a secure, tailored, always online and evolving access platform. It is a cloud service for modern security management. With CUMULUS we provide continuously up-to-date, data-secure access management products and software,” said Ahvalo.
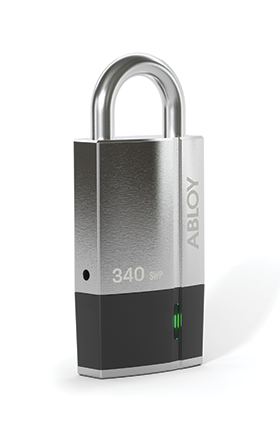
The first CUMULUS-branded products that will be available for customers later this year, include a padlock, a mobile application, a cloud-based software engine and application programming interfaces (APIs). The APIs allow integration to third-party applications such as booking, reporting, resource management and access control systems. New products will continuously be added to the CUMULUS range.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.