
The lockdowns, combined with the recent riots in South Africa have resulted in a lower demand for electricity. Of course, this is at the expense of the economy and jobs. Interestingly, these events have resulted in Eskom managing to keep the lights on for more of the cold winter days than expected. However, we cannot expect this to continue.
When a blackout, (load-shedding) occurs, households lose the ability to function properly. One of the consequences is that security systems fail. Not surprisingly, security service providers have seen this as an opportunity to sell battery systems to clients to keep alarms, electric fences and cameras going, while Eskom tries to restore power.
Solar power is an alternative to keep essential electronics running, but a solar installation costs from R50 000 upwards. Additionally, most people have no idea how much power they need to run various devices in their homes and what electrical components they need to ensure their safety or a reliable backup supply.
PowerBox is designed to provide enough power to keep the essentials running in a home or small business, for example, the security system, Internet (Wi-Fi) connection, PC and laptop(s), enabling life and security to continue during load-shedding.
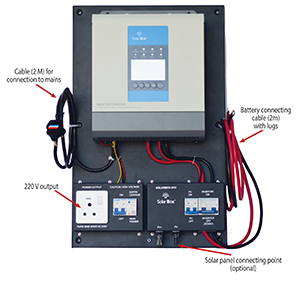
The idea was to develop a simple, robust product anyone can use, capable of an output of 1200 W continuously. The PowerBox comes with all the required technology on a single board, which can be attached to a wall, including the inverter, charge controller and output plugs.
It includes cables for connecting to batteries and a power cable to connect to the mains. Adding solar panels to the project to keep the batteries topped up is also an option.
A smaller 12 V – 800 W option (indicated below) will suffice for most blackouts that do not last for more than a four hours; however, if necessary a second battery can be added and connected in parallel.
Currently there are three PowerBox model options that will keep essential electronics, the basics for a home and small business running:
• 12 V – 800 W/20 A.
• 24 V - 1200 W/30 A.
• 24 V – 1600 W/30 A.
For example, a CCTV camera only consumes about 20 W on average, which means that with PowerBox one’s security system can still run without interruption, along with TVs, Wi-Fi, laptops and phone chargers.
A key practical benefit is that PowerBox can be wall mounted with four screws; plugged into the mains and the batteries are simple to connect. Even the optional solar panels are a simple plug-in. It’s designed to be a quick and easy plug-and-play DIY installation.
A further option is a connection to the home distribution board (DB), but this needs to be done by a qualified electrician.
Download the PowerBox brochure at www.securitysa.com/ex/PowerBoxHybridUPS.pdf or contact info@powerboxafrica.com, www.powerboxafrica.com
| Tel: | +27 11 543 5800 |
| Email: | malckey@technews.co.za |
| www: | www.technews.co.za |
| Articles: | More information and articles about Technews Publishing |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.