
Risk management and a security risk assessment are often seen as the same thing, when in fact, they are two vastly different things. The security risk assessor’s question is not if you have security, but rather if you have a security risk assessment. The general perception is that a security risk assessment and security is the same thing, however, these two concepts are two very different things, related, but different.

We believe that the risks need to be identified first before any management can take place. Security risk assessments specialise in the identification of security risks. The best way to describe a security risk assessment is as a ‘crime fighting tool’ and it only works if it is done independently. This consists of finding the security risks that provide opportunities for crime.
When conducting a security risk assessment, the assessor looks at outer crime as well as inner crime. Most people only look at outer crime and do not consider inner crime to be a concerning factor. In most cases, it is the inner crime factor that brings estates and companies to their knees.
A security risk assessment is an in-depth investigation into your current security measures to establish if there are any risks. When the risks are identified, the assessor finds suitable, risk-specific solutions to eliminate these risks. Some risks cannot be covered by security hardware; however, the assessor provides ample advice in the security plan that will eliminate these risks by means of processes, protocols and the application of security knowledge and understanding.
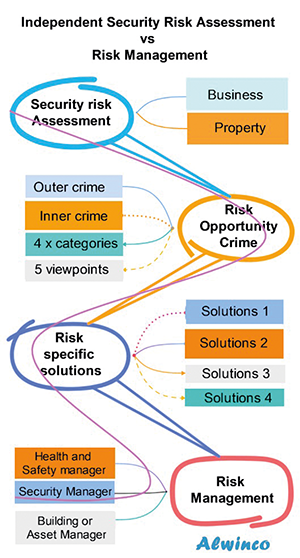
Once all the risks are identified and the assessor has found suitable solutions to eliminate the risks, he/she compiles all the information into a document that gets handed over to the client. When a security risk assessment report is read and understood, the risk manager can take over as he now knows and understands what the risks are and will be able to manage these risks in accordance with the security risk assessment.
Working under the risk manager, you will usually find a security manager, health and safety manager, building manager, and sometimes an asset manager.
When it comes to health and safety, we are dealing with the ‘probability’ or ‘likelihood’ of something, like an accident. A security risk assessment, on the other hand, looks at the opportunities for crime and when specific risks are identified, measures are put in place to manage these risks.
Keep in mind that the Health and Safety Act states that the business/company must ensure that no harm comes to employees or visitors. When this is interpreted correctly, the protection of employees and visitors includes security and crime as well. In South Africa, health and safety is governed by the law which means that it will automatically come first and take up most of the time and focus. Physical security is almost always neglected and left behind.
Neither of these aspects, whether it is risk management, health and safety, or physical security, are more important than the other. They are not the same, in fact, they are vastly different and should all be managed accordingly. In addition, health and safety, risk management and physical security must be managed by separate individuals and not one person alone.
If security is not managed as it should be, and the risks are not identified, the door is wide open for crime.
| Tel: | +27 87 148 8615 |
| Email: | andre@alwinco.co.za |
| www: | www.alwinco.co.za |
| Articles: | More information and articles about Alwinco |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.