
Effective security at the entrance should ideally allow for the quick, efficient and accurate entry of employees and visitors and should enforce predetermined access rules. Access control systems provide the means by which individuals are identified and these systems are used to specify such rules, whereas entrance control solutions provide the means of granting/preventing access.


Suprema’s extensive range of access control devices use various modalities such as face, fingerprint, mobile credentials, PIN and cards to authenticate users. These access solutions can be seamlessly integrated with various entrance control solutions such as turnstiles, speed gates and interlocking doors.
Suprema devices come with built-in door relays that connect to the relays of entrance control solutions such as turnstiles, speed gates, interlocking doors, boom gates, etc. If Suprema’s BioStar 2 is used as the security management platform, for example, the turnstile will be created as a door and no integration will be required for Suprema devices to work with the turnstile. However, if third-party software is used for the security management platform then the Suprema Device SDK will be needed to integrate the Suprema devices into the system.
Suprema also offers a range of controllers and other peripheral devices that can be used when setting up an effective solution for facilitating secure entrance.
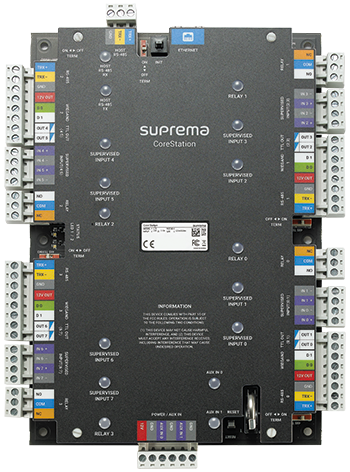
CoreStation is an intelligent biometric controller that enables centralised storage of user and access control data including fingerprint/facial credentials and is designed to accommodate enterprise-level systems of up to 500 000 users. It has a multi-port interface that supports locks, sensors, RTE and alarms. With CoreStation there is no Ethernet connection to the edge devices and there is no data stored on the edge devices. Communication is secured through TLS 1.2 and AES-256 encryption.
Door Module (secure multi-door I/O module) provides secure door control of up to four doors via encrypted communication and also contains two Wiegand reader interfaces for use with third-party readers. A wide variety of I/O interfaces allows Door Module to be a part of diverse system configurations. By combining Door Module with a Suprema device one is able to design and implement a centralised access control system with up to 32 doors and up to eight biometric devices through daisy-chain configuration.
Secure Module (compact secure single-door I/O module) provides secure door control via encrypted communication when combined with other Suprema devices. Its ultra-compact form factor allows it to be installed and used in different environments.
Output Module (multiple extension output module) is a multiple output extension module which can control up to 12 output relays. It can also be used as an elevator controller (up to 192 floors) with BioStar 2 system. A total of 31 units can be connected to a master device via RS-485 daisy-chain. The output module also has an anti-passback feature and a fire alarm feature.
With recent changes to health and safety regulations Suprema offers the following to assist in adhering to these measures.
Suprema Thermal Camera combined with Suprema face recognition terminals detect users with elevated skin temperature. The device displays the temperature on a GUI and raises alerts when higher than threshold temperatures are detected. Suprema Thermal Camera easily connects with Suprema face recognition terminals via USB interface. It comes with a bracket for convenient deployment on new and retrofit installs.
Suprema’s FaceStation F2 can detect users without masks and when integrated with an entrance control system can prevent entry without compliance. F2 also supports face recognition of users wearing masks.
| Tel: | +27 11 784 3952 |
| Email: | enquiry@suprema.co.za |
| www: | www.suprema.co.za |
| Articles: | More information and articles about Suprema |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.