
In the last few months, Check Point Research (CPR) focused on recent Windows Local Privilege Escalation (LPE) exploits attributed to Chinese actors. An LPE is used by attackers to acquire administrator rights on a Windows machine. During this investigation, our malware and vulnerability researchers managed to unravel the hidden story and origins behind ’Jian‘, an exploit that was previously attributed to the Chinese-affiliated attack group named APT31 (Zirconium). The attack tool was caught and reported to Microsoft by Lockheed Martin’s Computer Incident Response Team, suggesting a possible attack against an American target.
For the sake of brevity, we dubbed APT31’s exploit Jian. During this investigation, our researchers managed to unravel the hidden story behind Jian, which translates to a double-edged straight sword used in China. The Jian exploit was previously attributed to APT31 (Zirconium), and we’ve now discovered its true origins.
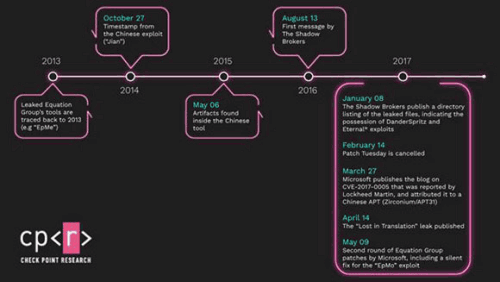
Our research shows that CVE-2017-0005, a Windows LPE vulnerability that was attributed to a Chinese APT, was replicated based on an Equation Group exploit for the same vulnerability that the APT had access to. EpMe, the Equation Group exploit for CVE-2017-0005, is one of four different LPE exploits included in the DanderSpritz attack framework. DanderSpritz is Equation Group's post-exploitation framework that contains a wide variety of tools for persistence, reconnaissance, lateral movement, bypassing antivirus engines, and more. EpMe dates back to at least 2013, which is four years before APT31 was caught exploiting the vulnerability in the wild.
In our technical blog, we introduce the four different Windows LPE exploits included in the DanderSpritz framework, revealing an additional exploit codenamed EpMo. EpMo, one of the exploits in the framework, was never publicly discussed and the unknown vulnerability it targets was patched by Microsoft in May 2017 with no apparent announcement. The patch could potentially be associated with the after-effects of the Shadow Brokers leak (https://blog.checkpoint.com/2017/05/25/brokers-shadows-analyzing-vulnerabilities-attacks-spawned-leaked-nsa-hacking-tools/) of Equation Group tools. While the vulnerability was fixed, we couldn’t identify the official vulnerability ID (CVE-ID) associated with it, and to our knowledge, this is the first public mention of the existence of this additional Equation Group vulnerability.
Read the full technical story at https://research.checkpoint.com/2021/the-story-of-jian

© Technews Publishing (Pty) Ltd. | All Rights Reserved.