
Data centres and IT facilities usually come in two flavours: off-site and in-house. However, in each case the common denominators are that an organisation’s data centre holds delicate and highly confidential information that requires the highest level of security. While today’s headlines are filled with hacking attempts to steal information off vulnerable networks and servers from remote locations, the threat of physical breaches into data centres is also real and requires a coordinated security strategy using a layered approach.
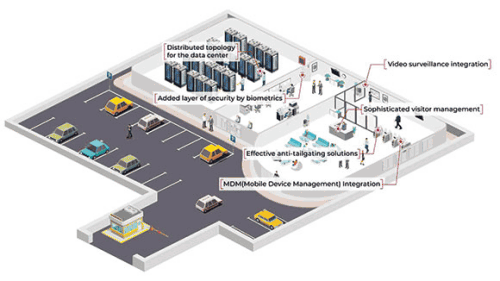
Whether the data centre is a remote, standalone facility or housed in a corporate location, it needs a protection plan that begins at the perimeter and moves to the building itself, then into the facility, the data centre or server room, and finally securing the cabinets and racks containing the wiring arrays and equipment. The security layers may feature perimeter barriers and surveillance, or secured entrances with high-level access control like mantraps and turnstiles, badging, multi-technology biometrics and analytics.
The size and shape of data centres varies according to the size of the organisations they serve, but each is the nerve centre of that company and prone to physical attacks. It is important to remember that many data centres are more than just information storehouses. The data centres contain essentials such as the wiring compartment room, which hosts the wiring infrastructure where network and systems alarms and firewalls are located, the computer/server room where the devices that perform the primary processing of a data centre are stored, and finally, the inner sanctum of the data centre, which is its data storage location.
While all of these areas are susceptible to remote virtual breaches, a physical breach into the data centre that destroys wiring infrastructure, or results in stolen servers or RAID drives, would be catastrophic for an organisation’s business health and operations.
Protecting data with access control
While physical security may not be the first thought in an environment of cloud computing and virtualisation, it should not be overlooked or underrated as a critical tool for cybersecurity. Controlling access to and within the building and its servers is critical to overall data centre security. By peeling away each layer within the building, the options available to help secure data centres are clear.
An immediate priority would be to limit access points into any facility housing a data centre, while keeping unencumbered exits required by fire codes. A high-security facility would require people entering the building to authenticate themselves a minimum of three times. Outer secured entrances to the facility could be a badge-in door with a buzzer or intercom system for guests. A sophisticated visitor management system would require guests to receive temporary access rights via mobile or RFID access cards tied to the access control system for tracking. In the case of a co-location facility, security revolving doors with anti-tailing sensor systems can be used.
Multi-factor authentication with any combination of face recognition, fingerprint, RF card and/or PIN is the best possible scenario. The access control system should allow for integration with video surveillance and have options for biometric authentication. Employing a level of flexibility in system design, differentiating authentication methods from the strict high-security access points to public areas with less restriction is an option. A high degree of separation and access must also be implemented, allowing access to only those who need it, and in the case of co-location, segmenting the rooms as much as possible.
The highest degree of security must be reserved for the data centre itself and it is here that a comprehensive anti-tailgating strategy is essential. Options include security revolvers (revolving doors) and personal interlocks tied into the building’s access control system. A security revolver may be equipped with a contact mat, scales (sensors to detect and prevent tailgating and piggybacking), or internal monitoring. A personal interlock or ‘mantrap’ would also work to prevent tailgating and piggybacking by only allowing one person through at a time.
Suprema recognises that your data centre is home to the most valuable assets of your company. Suprema’s latest biometric access control solutions are designed to meet stringent requirements from modern data centres. Combining the world’s leading biometric technology, distributed system topology, and integration with third-party solutions, Suprema provides the most secure physical access control solutions for data centres.
Suprema adheres to strict security standards:
Irreversible biometric template protection: Leakage of real fingerprint or facial images registered for authentication may pose a serious threat to security. Actual images are reorganised as binary templates through an advanced analysis algorithm which can never be reversed to a real live image.
Personal data protection: Protecting personal data from malicious attacks or leaks has never been more important. Suprema solutions are designed to safeguard all personal data including biometric credentials and any information that can be traced back to a user. All data is encrypted using AES 256, AES 128, DES/3DES before storing in the server, device or cards. Suprema’s web-based open security platform BioStar 2 also received ISO 27001 and 27701 certifications, satisfying international standards for data protection and management.
Communication protection against malware and data breaches: Communication protection using encryption and certificates is applied to all communications used in the system. Server to client communication is protected by HTTPS, which can use a trusted CA signed certificate. Between the server and device, all communications are encrypted using AES 256, which can be enhanced by using TLS 1.2. Serial communication through RS-485 is also encrypted using AES 128 under the requirement to secure all possible communications. These implementations result in a system where it can efficiently defend against malicious attacks and protect all sensitive data.
Physical protection of sensitive data on edge devices: All edge devices produced by Suprema support security tamper-proofing to protect stored data from physical threats. If any unauthorised attacker removes the device from the wall, all data and configurations stored will be deleted immediately.
Providing proof of compliance: All activity on the system is recorded from the moment of logging into the BioStar 2 platform. The operations are recorded as logs including information of time, object, and details of actions in the system.
Authentication for data access: The BioStar 2 platform faithfully reflects privacy protection and organisational operation requirements. Permission levels to access personal information can be divided up in various ways.
| Tel: | +27 11 784 3952 |
| Email: | enquiry@suprema.co.za |
| www: | www.suprema.co.za |
| Articles: | More information and articles about Suprema |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.