

As budgets get smaller, there is a trend for some to do as much of their security work in-house as possible, supported by, for example, how-to videos on YouTube and other sources. If you are installing a home camera system that may be all you need to get the job done, but what about larger and more complex jobs?
Is it still necessary to use an installer or system integrator (SI) when all you need is available on the Internet and much of the work has become IT work that more people are comfortable with? Hi-Tech Security Solutions asked a few local SIs why using a third party with experience is still the better choice than trying to do it yourself, or even trying to do parts of an installation yourself.

Gary Swart, Rhyco Risk Projects
The benefits of using a qualified professional
An organisation benefits nine times out of ten when using a qualified integrator rather than doing the job themselves. Below are some points to consider.
Planning: It starts with defining the requirement. What is the exact requirement? It is of vital importance to plan properly before any purchase is made or starting the installation. This also includes doing a proper wiring diagram, plan cable routes and the number of cables to use.
Once the requirement and routes have been established, with the help of the wiring diagram, the choice of equipment has to be made in line with requirements.
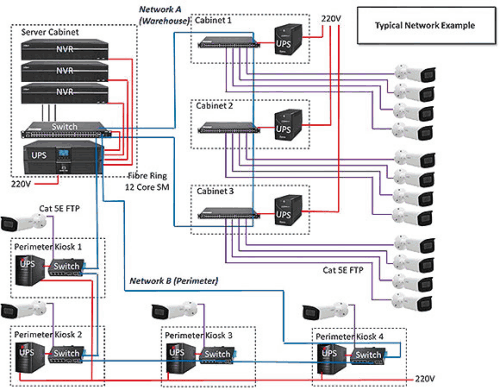
Figure 1 is an example of a diagram stating the requirements and amount of equipment that needs to be installed to meet the client’s requirement. It also forms part of network planning.
Wiring diagram and cable routes: By doing proper wiring planning, the correct sleeves and the amount of cable needed can be planned properly. Should the possibility of inference be considered, the correct cable can be purchased and the cable routes properly planned.
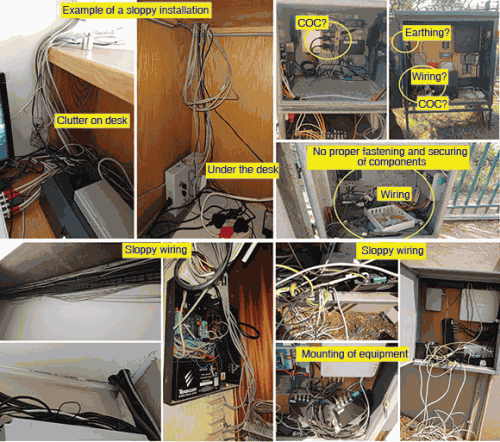
Installation: A proper installation does not just happen; it must be planned. Figure 2 shows some installations done by someone with the best of intentions. To list some of the typical problems occurring at client’s premises where installations have been done in-house: neatness, no cable markings, interference, earthing problems, incorrect equipment choices, and the list can go on. Unfortunately, when these bad practices cause a problem, they normally lead to additional costs for customers.
Which verticals does your company operate in?
Rhyco Risk Projects is an electronic security, risk consulting and integration company with local and international experience. We provide a turnkey solution, from risk assessments to security design, security equipment installations, fibre installations, integration, testing and maintenance. Our clients range from financial institutions, warehousing, factories, airports, oil storage facilities, housing estates, etc.
Are you finding that smaller specialist companies are being contracted to larger SIs for specialist work in large projects?
Rhyco Risk Projects found that some of our clients opted to accept quotes from lower-level companies to do installations as part of acquiring three quotations. As a company, we had to assist these clients with rewiring, marking of cables and in some cases complete reinstallations due to inferior work done. Unfortunately, due to lack of knowledge from such companies or to rush the project, failures occur regularly.
Rivash Raghubir, RR Electronic Security Solutions
The benefits of using a qualified professional
An electronic security systems integrator is a specialist service provider that brings together an array of essential components from different technologies and integration techniques to seamlessly function as a single platform solution. For example, bringing together the outputs from different systems to the security control room, such as CCTV, access control, intruder detection and perimeter systems.
There are many benefits of using a professional SI as compared to trying to build a solution internally. Some of the main benefits include:
• An organisation generally does not have the in-house expertise and skills to bring systems together as a complete solution as this would require using different OEM technologies and specialised integration techniques. In order to try to save costs, organisations try and use internal resources to provide a solution, which most of the time ends up actually doubling the project cost over a prolonged period of time to get the required solution – or in some cases, no solution at all.
The benefit of using an SI in this scenario is that it allows internal staff to stay focused on the core operation of the business while working in conjunction with the SI to provide a functional solution, taking into consideration the operational requirements and the system integrators expertise.
At the end of the day, working with an internal business / operational expert and a professional SI would save the organisation money and allow for a timeous, functional, integrated solution that works for the business and adds value.
• When a solution is integrated using different service providers or departments instead of a single SI, for example, an organisation uses their internal IT department to provide the software solution and the security department to provide the hardware for the integrated solution, this will, almost every time, end up a non-functional solution or an incomplete solution.
The first benefit here would be that an SI would be responsible for a complete solution with a single point of contact. A qualified system integrator will have the required expertise, tools and experience to rectify the problem, again referring to a single point of contact for the solution. A professional SI would take ownership of the solution and the support thereof, ultimately saving the organisation time and money.
• Many organisations nowadays seem to opt to deal directly with an OEM instead of a systems integrator for a solution, hoping to save costs on the overall solution. This poses a huge problem in the industry. An OEM is the master of his own system (a single system), an SI would have worked across a number of different industries and/or systems and operational requirements, and would be aware of integration best practices and specialised integration techniques.
An SI has the ability to see things from different perspective. This experience / expertise and outside perspective is what you are really paying for when you commit to a qualified systems integrator. Keep in mind that a systems integrator would have a professional two-way relationship with different manufacturers and system providers, while in most cases an OEM would turn to an SI for implementation ideas and integration techniques for a solution.
Which verticals does your company operate in?
We have experience in the following fields:
• CCTV
• Access control
• Intruder detection systems
• Electric fencing
Are you finding that smaller specialist companies are being contracted to larger SIs for specialist work in large projects?
Yes, we are receiving more requests to complete certain portions of work within a project that require specialised skill sets to successfully implement the whole solution. Specialised skills are definitely becoming harder to find as the smaller installers cannot afford to invest in engineering resources.
This scenario creates a huge problem in the industry as a whole, the reason being is that a qualified and experience SI cannot compete with an installer using lower levels of technicians. This directly effects the labour costing of a project.
Sharon Naudé, Bidvest Protea Coin
The benefits of using a qualified professional
The benefit is derived from the SI’s specialist knowledge and experience in designing holistic solutions. These solutions are interlinked and optimise the function of the individual security systems. As subject matter experts, in not only products and integration, but crime and risk prevention, reputable SIs are invaluable partners to organisations who are serious about security excellence. Furthermore large professional SIs, such as Bidvest Protea Coin, have the ability to offer various cost of ownership models, thus ensuring the maximum use and longevity is extracted from the customers investment.
Which verticals does your company operate in?
With decades of experience behind our name, Bidvest Protea Coin provides top-tier risk management though a variety of integrated solutions at our disposal. We are present in all vertical markets and enjoy dominance in banking, mining and telecommunications. Our client needs and risk profile determines the solution design, which could include any number of solutions These may include but not be limited to; surveillance, access control, time and attendance, underground cable theft detection sensors, perimeter barriers and protection, intrusion detection and verification and drone patrolling. With the inclination of the security market towards various IoT Platforms, our focus continues to be an alignment of our business to support Industry 4.0 and drive internal upskilling.
Are you finding that smaller specialist companies are being contracted to larger SIs for specialist work in large projects?
The move towards IoT and implementation of specialised solutions has encouraged a rapid increase in upskilling and acquisition of relevant knowledge within our business as a whole. Sales, operations, engineering and support all need a firm understanding of the solutions. Strategic engagement with specialist vendors is limited.
Owen Smit, ISF SFP
The benefits of using a qualified professional
ISF SFP is a systems integrator and makes use of various professional installers where required, interfacing various systems to provide the end user with a single point of contact for the many facets of complex installations, these include:
• Physical barriers, turnstiles, speed gates, vehicle systems
• Network providers, fibre installations
• BMS integration
• Onboarding staff via payroll
• Licence plate recognition integrated to access control
• CCTV analytics
Which verticals does your company operate in?
ISF SFP operates in the commercial and industrial verticals providing the end user with an integrated solution, we are well versed in fire detection, fire suppression, access control and CCTV, having rolled out several national projects for corporate customers.
Are you finding that smaller specialist companies are being contracted to larger SIs for specialist work in large projects?
We are finding a lot more smaller companies being contracted in for specialist work as technology evolves, it is smarter to use these focused specialist to provide the end user with a solution which could range from sophisticated visitor management systems to parking solutions, all reporting to a single platform with various methods for users to transact.
| Tel: | +27 12 665 8000 |
| Email: | info@proteacoin.co.za |
| www: | www.proteacoin.co.za |
| Articles: | More information and articles about Bidvest Protea Coin |
| Tel: | +27 11 794 2825 |
| Email: | info@rress.co.za |
| www: | www.rress.co.za |
| Articles: | More information and articles about RR Electronic Security Solutions |
| Tel: | +27 11 543 5800 |
| Email: | malckey@technews.co.za |
| www: | www.technews.co.za |
| Articles: | More information and articles about Technews Publishing |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.