
We are aiming to educate those in leadership positions about the importance of commissioning regular independent security risk assessments. As a security advisor, it’s a continuous challenge to change the existing perceptions of CEOs/MDs and nowadays the procurement departments.
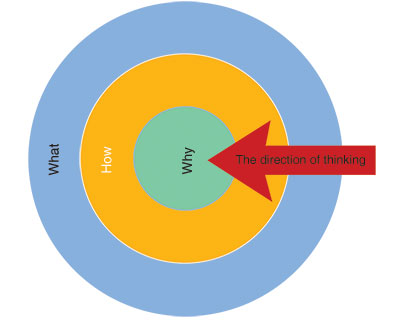
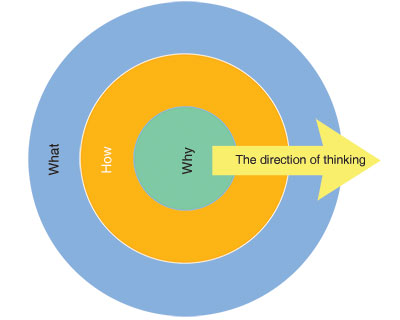
The two diagrams in this article both contain the exact same words, however, the only difference is the direction of the arrow which indicates the thinking pattern.
The first graph shows the thinking direction from the ‘what’ inwards to the ‘why’, whilst the second graph shows the thinking direction from the ‘why’ outwards to the ‘what’.
Most people approach security from the outside in, as displayed in the first graph. The ‘what’ in this case mostly refers to a product and this needs to be answered with ‘how’ and ‘why’.
What security products are we going to sell?
How will we accomplish this? This could either be how the salesperson will get the client to purchase the product, or how the product will be installed.
The ‘why’ refers to why do you need this specific product, why do you need to have it installed? Why will this product be effective?
The last part of this thinking direction, the ‘why’, will most probably not be answered because the action has already been taken. The product has been purchased and installed; the ‘why’ doesn’t really matter now anymore, does it?
It’s like spending money on a new pair of expensive running shoes because you get a free water bottle or a gym bag with your purchase. You purchased the shoes thinking about the freebies without really knowing why you need it. Even if you think about the ‘why’ later, it wouldn’t matter because you already purchased the shoes.
It might be the wrong running shoes for the type of running you do, or it might not be the right shoes for your feet. You will end up wasting a lot of money because you did not think about the ‘why’.
Turn it around
Now, in contrast with the first graph, the second one shows an outward thinking direction. This means that you are looking at and thinking about security from the inside towards the outside.
The first question you will ask is why do I need security? Simple: to cover your risk.
The next question will be how will we achieve the ‘why’? The ‘how’ question is answered with an independent security risk assessment. An independent security risk assessment will tell you what your risks are, and it will tell you how to fix it.
The last question, ‘what’, is also answered in the security risk assessment. What do you need? The solutions in the risk assessment will tell you exactly what you need.
Remember the running shoes? Well, when you think about it from the inside outwards, you will understand why you need running shoes. Your answer will depend on what type of running you do; for example, you might be into trail running, marathons or road races.
The different types of running will tell you what running shoes you need. How do you get those shoes? You go to a specialised running shoe store that specialises in the type of running shoes you are looking for.
Knowing why you need it and how to get it will ensure that you know exactly what to get, even if other shoes are on special or if you get heaps of freebies with walking shoes, you will know that you need trail running shoes as this is what serves your purpose best.
The same applies to security
When you understand why you need security (to eliminate your risk), how it is achieved (by implementing risk-specific solutions), you will understand exactly what you need to accomplish this (informed decision making when it comes to security hardware).
Practically, when you think from the outside inwards, you are thinking about the product first, which is the approach most security salespersons and security companies take. Thinking about the product without knowing what it needs to do in order to eliminate the risk could result in a waste of money, or worse, a false sense of security.
Believing that you are safe due to your security measures without knowing if it really covers your risks is far worse than having no security at all. When you don’t have any security and you know the dangers, people tend to be more vigilant and aware of their surroundings. On the other hand, when you think you have security and that you are safe, you become lax, complacent and oblivious to your surroundings, which is a very dangerous situation to be in.
This is the difference between a security company and a security risk assessor’s approach to security:
• A risk assessor starts from the inside, finding the risks and then moving on to find the solutions that fit the risks, not the other way around. The risks cannot be forced to fit the solutions.
• You are welcome to disagree, all I ask is that you show me the security risk assessment of your current security.
If you are thinking from the inside to the outside, you are thinking about what the client needs to eliminate the risk. However, when you think from the outside inwards, you first have a product in mind without considering the risk, which does not put the most important factor, the client, first.
Whilst the questions might be the same in both scenarios pertaining to the ‘why’, ‘how’ and ‘what’, the direction makes all the difference. In both graphs, the ‘how’ is in the middle, however, when you start from the inside, the ‘how’ will apply to the client whereas when you start from the outside, the ‘how’ will apply to the product.
| Tel: | +27 87 148 8615 |
| Email: | andre@alwinco.co.za |
| www: | www.alwinco.co.za |
| Articles: | More information and articles about Alwinco |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.