
Integrated access control solutions deliver impressive functionality, yet there is a significant requirement for seamless integration and the application of intelligent framework solutions that empower educational institutions to unlock considerable value by integrating disparate systems. Detailed blueprint design, including business process mapping and detail technical and functional requirements definition is key for successful delivery to the various stakeholders.
In addition to schools, educational institutions such as universities and colleges present a unique challenge with regards to application of security technologies.
Campus architecture and design has historically been towards open facilities for learning. The increasing need to provide a secure environment for students has placed significant pressure onus on academic institutions as has the global trend towards smart campuses where technology innovation allows for a secure environment without creating an impression of locked down facilities.
Challenges in educational institutions
Implementing a seamlessly integrated access and security solution in a corporate or manufacturing environment is often a significant challenge. In a dynamic and ever changing environment such as universities/colleges where change is not only limited to student turnover the challenge is significantly increased.
Typically, installed security systems are secure at the time of installation, but over time the database accuracy is degraded as access rights that should be managed by group policy are allocated to individuals based on urgent needs or physical location and actual changes are not configured on the system. Processes such as terminations, course changes, location changes for lectures and classes are not automatically applied and the recording of attendance to these classes by students (sometimes a statutory requirement) is reduced to a manual paper trail with no consolidated reporting benefit.
With a global focus on corporate governance and specifically governance, risk, and compliance (GRC), all aspects of an organisation are directly or indirectly impacted by heightened security policies and procedures. These new business requirements demand that non-security functions (HR/IT/finance/facility/wellness and even logistics, etc,) become directly accountable for identity management and policy enforcement.
In educational environments, the various inputs required to allow access or record attendance can become extremely complex.
Ownership of source data input, for example, has effectively transferred accountability from the security function to whoever is accountable for the relevant business process and mandated for the correct capture of the source data.
If one applies basic real-life processes and scenarios to this data, it could mean that a student’s access to site or a specific area is dependent on multiple people in an organisation providing an holistic framework for a process driven solution:
* His/her master data being valid (Student Admin) – data might even reside in disparate systems,
* Payment of accounts being valid (Finance),
* Course content allowing usage of computer labs (IT) and
* If driving a university vehicle that their driver’s licence is valid (Safety).
Legacy options
Common practice is to isolate an organisation’s people data into numerous applications such as payroll, time and attendance (T&A), HR, access control, enterprise resource planning (ERP), user access (IT) and many other systems. This gives great flexibility to the organisation in allowing the use of best-of-breed solutions, each addressing specific needs.
The problems created with this approach when applying physical and logical security policies and systems is:
* No single system has a true (single version of the truth) view of all the people data and relationships within the organisation (students/employees/contractors/service providers/visitors etc).
* Due to the disparate nature of these applications, sharing of data is often dependent on specialist interfacing skills or manual processes such as e-mails containing report extracts to spreadsheets and labour intensive importing of files and/or interfaces. The systems can be subject to a high level of erroneous data – for example, names are spelt incorrectly, identification data is mistyped for the same person across the different applications.
* Data is often out of date. Administration or HR terminates a person in its system, but they remain active on the other systems.
* Each system has segmented data specific to a functional need. For example, HR is only interested in employees and contractors, IT is only interested in users and security wants to know about everybody including visitors.
* Security risks are increased when systems are not seamlessly integrated and linked according to process.
When these issues are combined, the problem becomes exponentially more complex. Systems integration can solve some of these issues, but often lacks the flexibility to change in line with the organisation or is vendor specific.
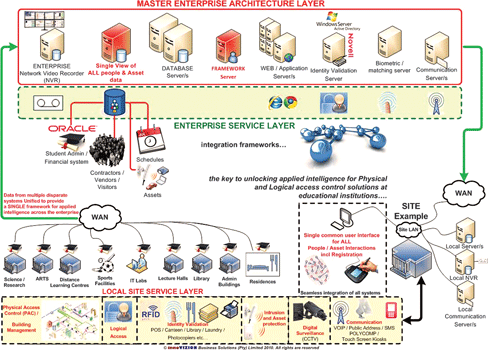
Annual churn of student data and allocation of access rights to students based on course selection etc. would possibly be manageable by interfacing an authoritative system (such as a student management or accounting system) to a new access control solution. However, when an holistic view of the requirements is taken it is clear that no single system will cater for all the stakeholder needs. Figure 1 is an example of an application architecture landscape of an integration framework that applies process driven access control solutions at an academic institution.
For more information contact innoVIZION Business Solutions, +27 (0)11 463 0123, [email protected], www.innovizion.co.za
© Technews Publishing (Pty) Ltd. | All Rights Reserved.